Download Product Brochure
SBOM Studio
.svg)
.svg)
.svg)

Software Bill of Materials: SBOM Studio
Gartner estimates that upwards of 80 percent of modern software incorporates open source libraries (OSS) or components from third-party upstream suppliers into product design. These pre-made components increase productivity and shorten development time, but they also introduce risk into the final product. Like any software module, these ingredients can contain vulnerabilities that emerge over time, making the overall software product less secure and reinforcing the need for continuous risk monitoring.

At every stage of the software development lifecycle (SDLC), Cybeats can extract the characteristics and attributes from software SBOM, even without access to source code, to deliver deep insights into the quality and security of software components.
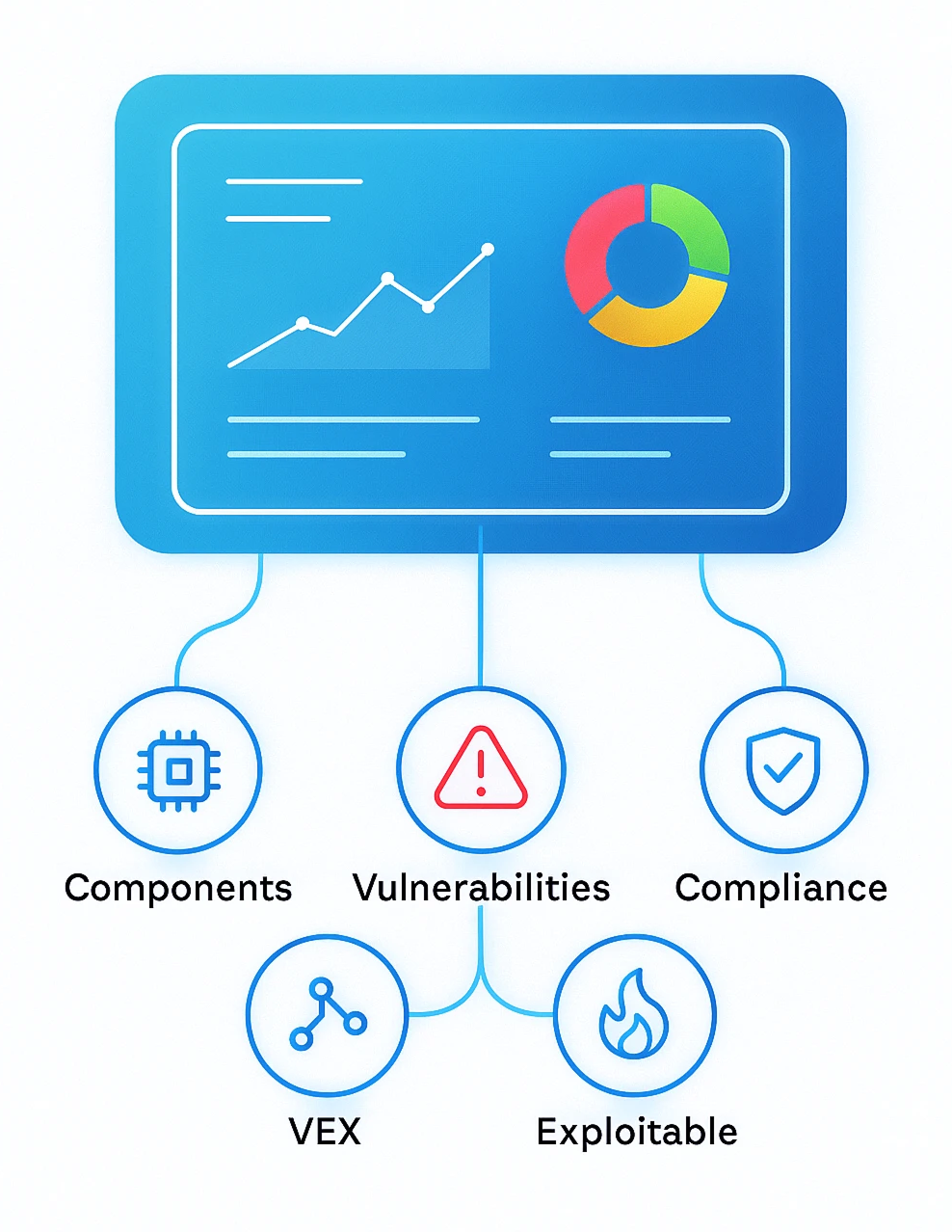
SBOM Studio is the Management Solution for your Software Security Lifecycle
Cybeats SBOM Studio is an enterprise-class solution that helps you understand and track third-party components that are an integral part of your own software. Use SBOM Studio to document what you have and where it came from, and plan for the maintenance that will prevent security posture degradation over the life of your software.
.png)
.png)
.png)
.png)
.png)
Key Features

Coming into effect for the sharing of SBOMs are Industry regulations which mandate fines for non-compliance or shut down operations completely.
The first step in mitigating these risks is the ability to inspect all the software that comes from suppliers into your supply chains. In industries where safety and security are paramount, it is not economically feasible to manually inspect all third-party files to ensure the quality of a multi-tier software supply chain.
The time is now to develop a business advantage by putting the systems in place to manage and share SBOMs.

Organizations have a need to iterate and deliver software rapidly. Software that would take up to a month to complete can now be automatically remedied within minutes with Cybeats. A documented SBOM provides the ability to forecast costs for cybersecurity over the product lifecycle and allows the business to properly budget and allocate resources to maintain an advantage over security threats.
.svg)
Create transparency and build trust across your software supply chain by sharing SBOMs with customers and receiving SBOMs from technology providers. Immediately understand the risks inherent in your products and mitigate as needed.
Who Needs SBOM Studio?
SBOM Studio is a versatile solution with many levels of sophistication. It provides high level data and metrics for executives and managers and can go deep into the nuts and bolts for software developers. Who can benefit from using SBOM Studio?

Industrial control system (ICS) environments who need to reduce cyber risk to ICS infrastructure, and gain compliance with ICS cybersecurity standards.

Operational Technology (OT) operators looking to reduce intrusions and protect their systems from disruption.

Medical device manufacturers and healthcare delivery organizations like hospitals whose patients use life-saving devices with embedded software.
.svg)
Developers, product managers, and security officers who must ensure the secure design and ongoing function of any software product, including code embedded in various hardware devices.

Company executives who want to thoroughly understand the risks inherent in their software products and future costs for maintenance.

Any entity that sells or plans to sell software products, equipment, or devices with embedded software to the U.S. military or a U.S. government agency (compliance with Executive Order 14028).

Enterprise organizations and government agencies that utilize software from external vendors.
.svg)
Anyone who makes use of a software supply chain that isn’t under their full control.
Want to learn more about vulnerability lifecycle management?
.svg)
in vulnerability management.
.svg)
identification, prioritization, and remediation.
.svg)
effective vulnerability management processes.
By entering your email, you agree to receive marketing emails from Cybeats. You may unsubscribe from these communications at any time. View our Privacy Policy for more information.

SBOM Lifecycle Management
.svg)
See Cybeats Security Platform in Action Today
We shortened our vulnerability review timeframe from a day to under an hour. It is our go-to tool and we now know where to focus our limited security resources next.
.svg)

SBOM Studio saves us approximately 500 hours per project on vulnerability analysis and prioritization for open-source projects.
.svg)


.svg)
.svg)